- InfiTip provides a GUI where multiple teams can collaborate in real-time and role-based access can be provided for restricted or entire access.
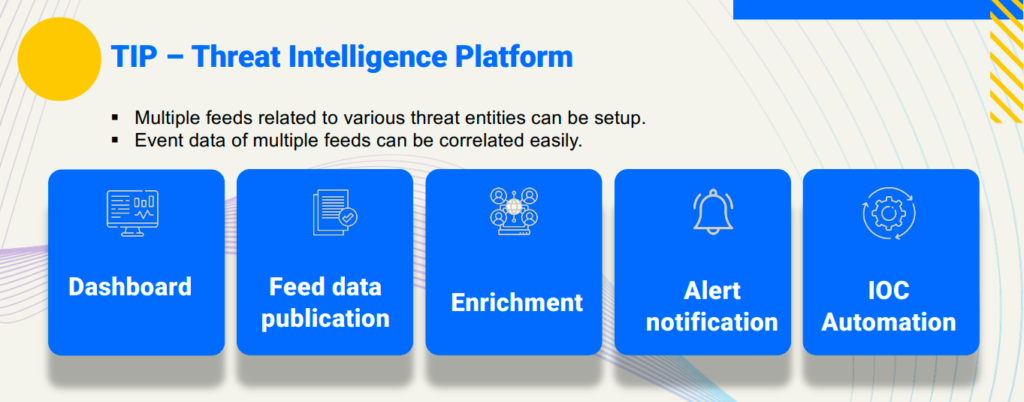
Infitip platform provides sharing, storing and correlating, threat intelligence and vulnerability information. Additionally, this makes use of information and IoCs to identify and prevent risks, fraud, or threats on ICT infrastructures, organisations, or individuals.
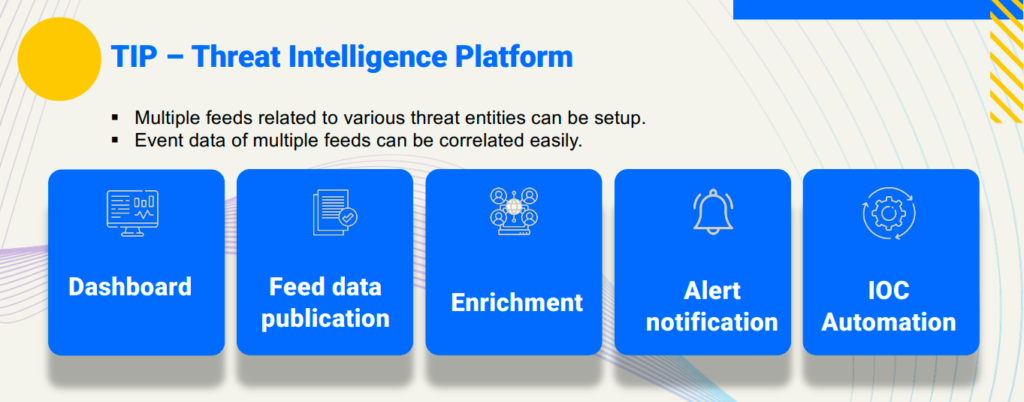
2. It provides a single platform for threat data aggregation/consumption from multiple vendors and different data sources like 3rd party blogs, articles and feeds. Moreover, it also allows to publish data to such kind of sources.
3. The 3rd party data can be plotted on a timeline and data enrichment can be done. It also allows to enrich data using
various 3rd party options like MISP, Maxmind etc.
4. It can work on VMs or as a standalone system. It can also work in an AIR gap system. User can create custom dashboards.
5. It allows the user to set various indicators and custom tagging for the attributes. The scoring of indicators is also
possible.
6. It allows to setup custom playbooks that run through native integration with leading industry SOAR platforms.
7. It provides ability to integrate with various data sources like SIEM, SOAR, TIP and ticketing systems
8. It supports various data models and standards by allowing the user to define and make use of taxonomies.
9. Data from standard formats like TAXII, STIX1.x and STIX2.x can be imported and exported.
10. It allows to do basic search based on keywords, filters as well as advanced search using operators like arithmetic and boolean. In addition, you can save the searches too.
11. It provides detailed analysis and reports of the data collected using various sources. Moreover, the timestamps are set for every piece of data which facilitates historical analysis and reporting including duration based searches.
12. The entire data management like import, export, search is possible using the APIs and SDKs. Thus, seamless integration is possible.
13. All the additional attributes and contexts provided by the threat intel sources can be parsed and stored. Search and filtering is possible for these additional attributes and contexts.
14. It supports manual upload of TTP and IOC and can extract and categorize indicators from such uploaded data.